 On November 24, 2021, Chinese technology giant Alibaba notified Apache Software Foundation of a flaw in its log4j software that has existed for years. It took approximately two weeks for Apache to develop and release a fix.
On November 24, 2021, Chinese technology giant Alibaba notified Apache Software Foundation of a flaw in its log4j software that has existed for years. It took approximately two weeks for Apache to develop and release a fix.
In that time, news of this recently discovered cybersecurity vulnerability began to spread across the internet, indicating that one of the most popular pieces of computer code in use today, log4j, contained a series of vulnerabilities that threatened millions of systems relied upon by many, if not most, of the largest and smallest businesses in the world.
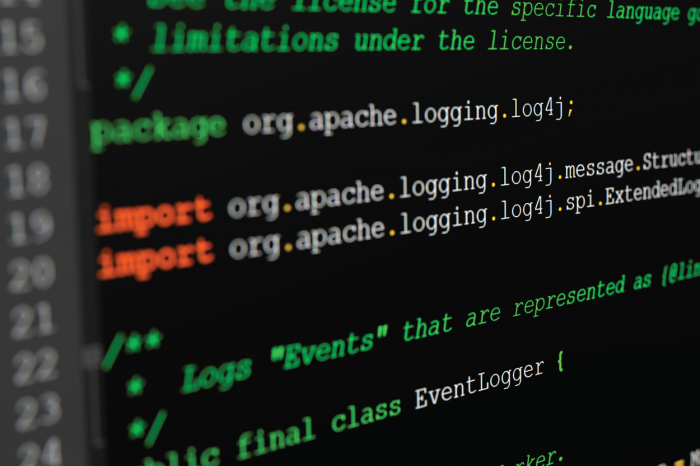
Log 4j
If you haven’t heard of log4j or this newly discovered vulnerability, you’re probably not alone. Log4j is a piece of code that helps software applications create libraries to log and keep track of their activities. It is written in an old programming language called Java and is designed to log activity for applications. Think of it as the trip computer on your car; it simply runs in the background and helps create a library of activity to help with troubleshooting and performance.
Log4j was developed by a handful of volunteers under the open-source Apache Software Foundation and is quite a popular logging application used by innumerable commercial applications. When developers are writing software, log4j is an easy to use and freely available application that can be “plugged in” so that developers do not have to create their own logging applications from scratch.
This is like buying an off-the-shelf part instead of machining your own. Log4j has been considered extremely reliable because it has been subject to years of user testing and rigorous use and implementation around the world.
Daily Use Applications
Major portions of computer code in applications that are used in business and daily life rely on log4j. Even cloud storage systems, which provide the digital infrastructure for most applications, are impacted by this vulnerability, including software and tools that are used by millions of people every day. This even includes smart devices, smart TVs, and security cameras.
Given how widely log4j is used, bad actors who try to breach digital spaces or steal information have more opportunity to do so because this vulnerability opens up an avenue to slip into places they otherwise could not go. The opportunities to breach otherwise inaccessible systems and steal otherwise inaccessible information are much greater than they were before.
Businesses are advised to engage cybersecurity experts to vet the systems they use for log4j, and if log4j is in use, to check for exploitation and patch any vulnerabilities.
Multiple Threats
Already, the U.S. Cybersecurity and Infrastructure Security Agency indicated that this Java-based logging library was being actively exploited by multiple threat actors. Immediately, almost every major software company in the world was engaged in identifying whether their products and services were impacted and working to mitigate those vulnerabilities.
Many are still trying to figure out whether their software uses log4j, and if so, whether their applications were exploited. Exploitation of these vulnerabilities is extremely serious because the bug essentially allows an unauthenticated actor to remotely execute code on a server. This means that exploitation can occur even if the software accepting data input is not written in Java by allowing the passage of malicious strings to other systems that are written in Java.
Given the ubiquitous use of log4j, this vulnerability threatens software used by millions of people every day and puts sensitive information and systems at great risk.
The global community of programmers and cybersecurity experts have been working to try and fix the vulnerabilities in whatever software they are responsible for. Technology firms are dedicating immense amounts of human power to manually review millions of lines of code to make sure systems are safe. Small businesses are contacting their software vendors to seek clarity and updates for existing programs. And this process will be repeated until the majority of the vulnerabilities to log4j have been resolved.
Ongoing Challenge
Importantly, the issue is not one that can be solved at once permanently. Cybersecurity is a series of redundancies and requires ongoing work into perpetuity. This is because cybersecurity is effectively a race against bad actors.
While companies continue to get better at protecting their systems and users, bad actors, particularly state-backed bad actors, continue to gain intelligence and improve their tactics.
The reality is, the real harm that may result from the log4j vulnerability may not appear until a year or two later, when bad actors have had a chance to choreograph and execute more coordinated, targeted, and harmful attacks against vulnerable systems. Thus, it is a race against time to try and fix any remaining bugs, update systems, and identify exploitation where it has occurred.
This article appeared originally as a Capitol Insider blog post.